Vishing: how Hucency invented the first mnemonic device to combat this type of attack
Vishing, or voice phishing, is an increasingly common and sophisticated social engineering attack.
It aims to trick a user over the phone into revealing sensitive information or taking urgent action that benefits the attacker.
In response to this threat, Hucency is breaking new ground: we have created V.I.S.H.E.R., a unique mnemonic device dedicated to cybersecurity, offered to our clients and designed to become a universal reflex against phone-based attacks.
Hucency, a key player in the fight against vishing
Hucency observed that mnemonic devices are widely used to reinforce reflex actions in certain institutions (emergency response, the military, etc.), such as P.A.S. (Protect, Alert, Assist), C.C.C. (Collar, Tie, Belt), and many others.
Until now, there was no mnemonic device available to combat social engineering over the phone. That is why Hucency developed V.I.S.H.E.R.
With V.I.S.H.E.R, Hucency is emerging as a key player in raising awareness about cyber threats, offering a practical tool that is accessible to everyone.
Our goal is clear: to make V.I.S.H.E.R. a go-to resource—not only for businesses and their employees, but also for institutions and government officials—so that anyone faced with a request for sensitive action has a simple and effective tool at their disposal.
V.I.S.H.E.R.: a simple mnemonic to remember
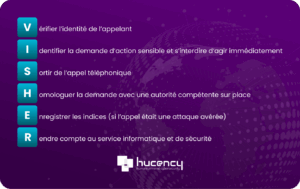
The V.I.S.H.E.R. mnemonic consists of 7 clear and easy-to-remember steps:
-
V: Verify the caller's identity
-
I: Identify the request for immediate action and refrain from acting immediately
-
S: End the phone call
-
H: Have the application approved by a competent local authority
-
E: Record the evidence (if the call was a confirmed attack)
-
A: Report to the IT and Security Department
A simple training tool designed to help employees protect their organization in real-world situations.
The right steps to take when receiving a call involving a sensitive request
In addition tothe V.I.S.H.E.R. mnemonic, it is essential to incorporatebest practices:
-
- Take a moment to restate the purpose of the call and the caller’s identity.
(Hucency Council) This helps you better assess the situation and saves time, allowing you to better manage the phone conversation.
- Take a moment to restate the purpose of the call and the caller’s identity.
-
- Treat any request for immediate action as suspicious.
(Hucency Tip) Attackers need to act quickly to better achieve their goals. The use of a pretext that creates a sense of urgency is inherently suspicious.
- Treat any request for immediate action as suspicious.
-
- Report any unusual behavior to security services.
(Hucency Council) Some seemingly harmless calls are actually used to gather information. This step is often the starting point of an attack.
- Report any unusual behavior to security services.
-
- Perform a double-check.
-
- Learn to clearly distinguish between internal and external calls.
(Hucency Tip) Warning: You may encounter number spoofing. This underscores the importance of the other V.I.S.H.E.R. protocols.
- Learn to clearly distinguish between internal and external calls.
-
- Systematically check any emails or messages related to the call (sender, urgency, context).
(Hucency Tip) A fraudster needs user interaction to proceed. These interactions may include:
– a request to take action on an item sent by the attacker;
– a request to send informationto a recipient specified by the attacker;
– a request to disclose confidential information.
It is therefore essential to verify the nature and content of these interactions.
- Systematically check any emails or messages related to the call (sender, urgency, context).
-
- Remember that it is perfectly acceptable to ask your conversation partner questions or to ask them to wait while you verify their identity.

A future standard in cybersecurity?
With V.I.S.H.E.R, Hucency aims to ensure that users and organizations are not left without solutions when faced with social engineering.
Because cybersecurity depends first and foremost on people, Hucency once again places the user at the heart of digital defense. In this way, every employee becomes a strong link in the chain of collective security.
Conclusion
Vishing is a growing threat and, as a result, requires appropriate countermeasures.
With V.I.S.H.E.R, Hucency offers a unique, simple, and universal tool that could one day become the standard for raising awareness about phone attacks.
Cybermois Special Offer
To celebrate Cybermois, we invite you to try the Vishing Pentest for free and with no obligation.
Sign up using our form:
Contact our vishing expert
Would you like to learn more about vishing and find out how to protect your employees from this type of attack?
Our Hucency experts are here to help.
Please contact our Vishing Manager directly to:
-
get personalized advice,
-
ask questions about the V.I.S.H.E.R. mnemonic,
-
or set up a vishing penetration test tailored to your organization.