What does cybersecurity have to do with Valentine's Day?!
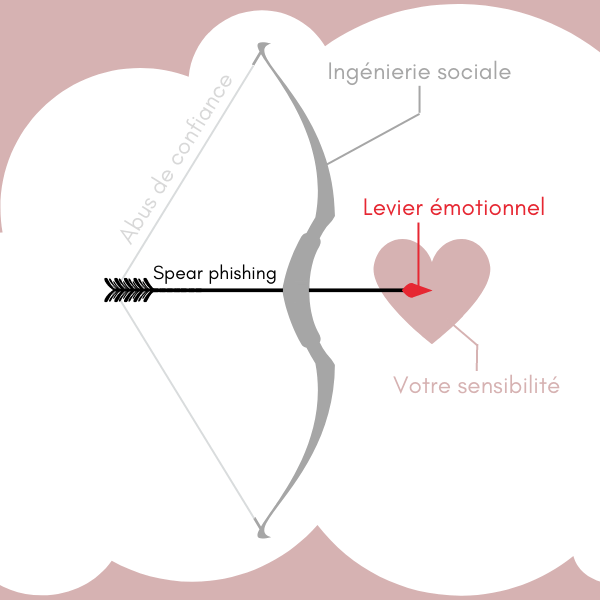
Valentine's Day is synonymous with love and celebrates the beauty of human relationships. Unfortunately, it also means that online scammers can take advantage of this period of emotional openness to launch spear phishing attacks using social engineering and even tools such as deep fakes.
During Valentine's Day, but also on other days of the year, scammers may target singles online using so-called "online romance" scams. They may pose as an attractive and interesting person to gain the trust of singles online, encourage them to share intimate information or content, and/or abuse that trust to extract money from them.
Scammers may also target retail businesses that have special Valentine's Day promotions. They may send phishing emails or messages that appear to come from these businesses, prompting victims to click on dangerous links or provide sensitive information.
Dating apps are an ideal playground for hackers
Be careful about the information you share with people you meet on dating apps, as you could end up "matching" with a cybercriminal. Hackers have many opportunities on dating sites and apps. It's easy to start a conversation there, and these malicious individuals can exploit your desire to meet someone for their own ends. The opportunities are endless:
Data collection – Hackers can collect information about users by posing as authentic individuals on the dating app. They can use this information to launch targeted attacks or commit fraud.
Phishing – Hackers can use phishing techniques to trick users into clicking on links that take them to sites designed to collect sensitive information such as passwords or credit card details.
Malware propagation – Hackers can use dating apps to distribute malware such as viruses or spyware by posing as potential partners.
Scams – Hackers can also use dating apps to carry out online scams, such as requesting funds for a supposed emergency or in exchange for services that may or may not be legal.
In this context, cybercriminals may use other practices and levers:
Focus on a particularly vicious practice used by cybercriminals: sextortion.
-
What is sextortion?
Sexual extortion, also known as sextortion, is a form of blackmail in which a person threatens to disseminate intimate or compromising information or images to others if the victim does not provide what is requested. This may include money, other sensitive information, or the performance of actions in the workplace, for example.
Sextortion can occur in various ways. For example, a person may be threatened with the publication of intimate photos or videos obtained as a result of an online relationship or correspondence via a dating app, for example. It can also involve malware that captures sensitive information or images on the victim's computer and uses them to blackmail them.
-
How should you respond to a case of sextortion?
It is important to note that sextortion is a form of online violence. Victims of sextortion may experience significant stress and feelings of humiliation, which can have long-term repercussions on their mental health. It is therefore important to seek help from a professional in this field. On the other hand, avoid any contact with the extortionist to avoid encouraging demands for payment or information. Nevertheless, it is recommended that you keep all evidence of sextortion, such as emails, messages, or screenshots. This may be useful to the authorities. We recommend contacting the authorities to file a complaint against the perpetrators of this sextortion.
CIOs, CISOs, DPOs, request a free demonstration of the fully automated phishing awareness solution: