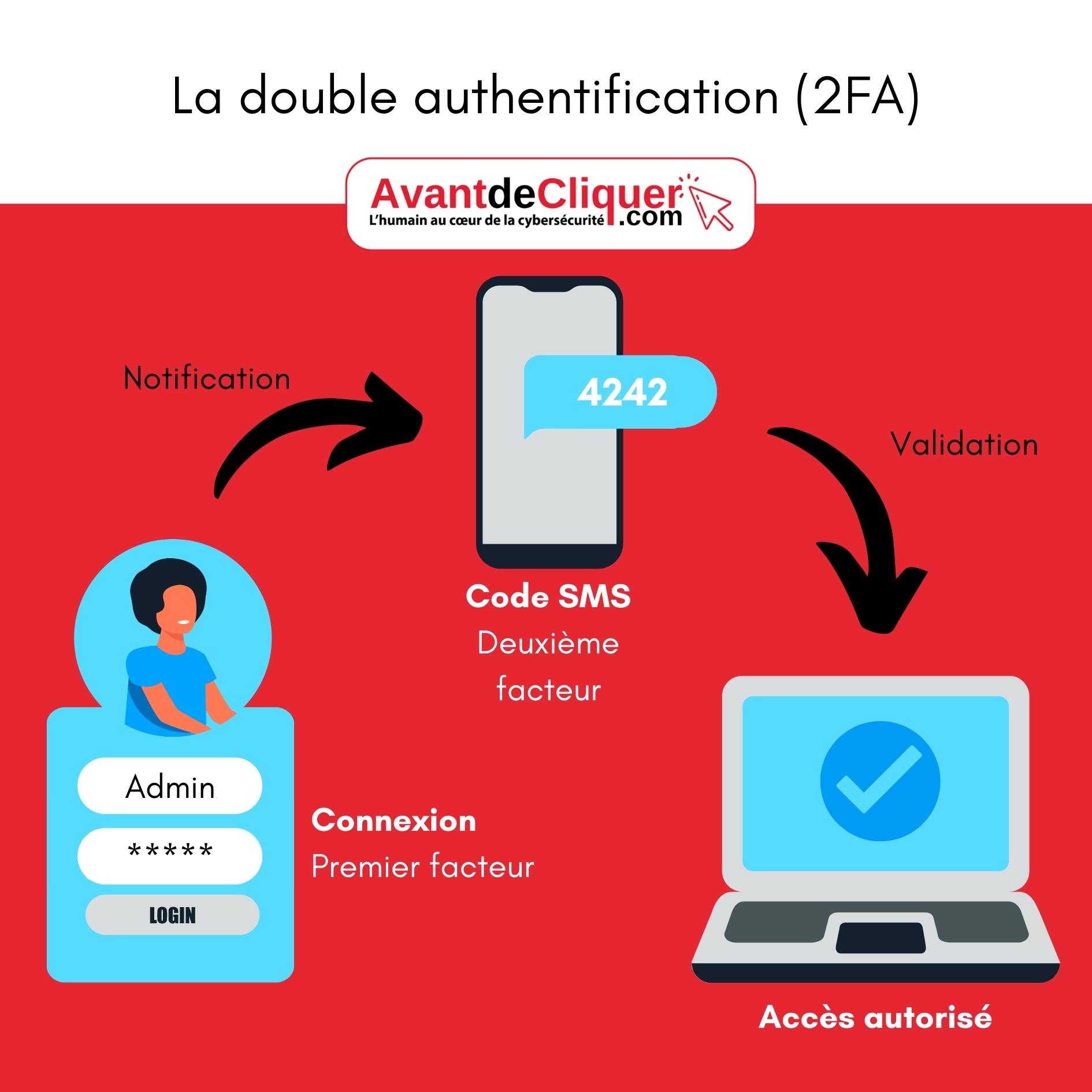
Definition: two-factor authentication or two-step verification
2FA, also known as multi-factor authentication, is a security process whereby the user provides two forms of identification from separate categories of data.
- First factor: usually in the form of a physical token, like the information on your credit card.
- Second factor: in the form of single-use information, such as a security code.
What exactly is the second authentication factor?
Here are some examples of second factors for two-factor authentication:
- Sending a unique code via text message;
- Using an authentication app (such as Microsoft Authenticator or Google Authenticator);
- Emailing a code that can be used for a limited period of time;
- Use of a rolling code with validation on another device;
- Using an authentication USB key
- Unlocking via a Bluetooth signal (via your smartphone, for example)
As you already know, hackers are adept at finding vulnerabilities and bypassing security systems, whatever they may be. In fact, more and more cybercriminals are managing to get around this 2FA and easily infiltrate our accounts to steal confidential data.
How do hackers bypass two-factor authentication?
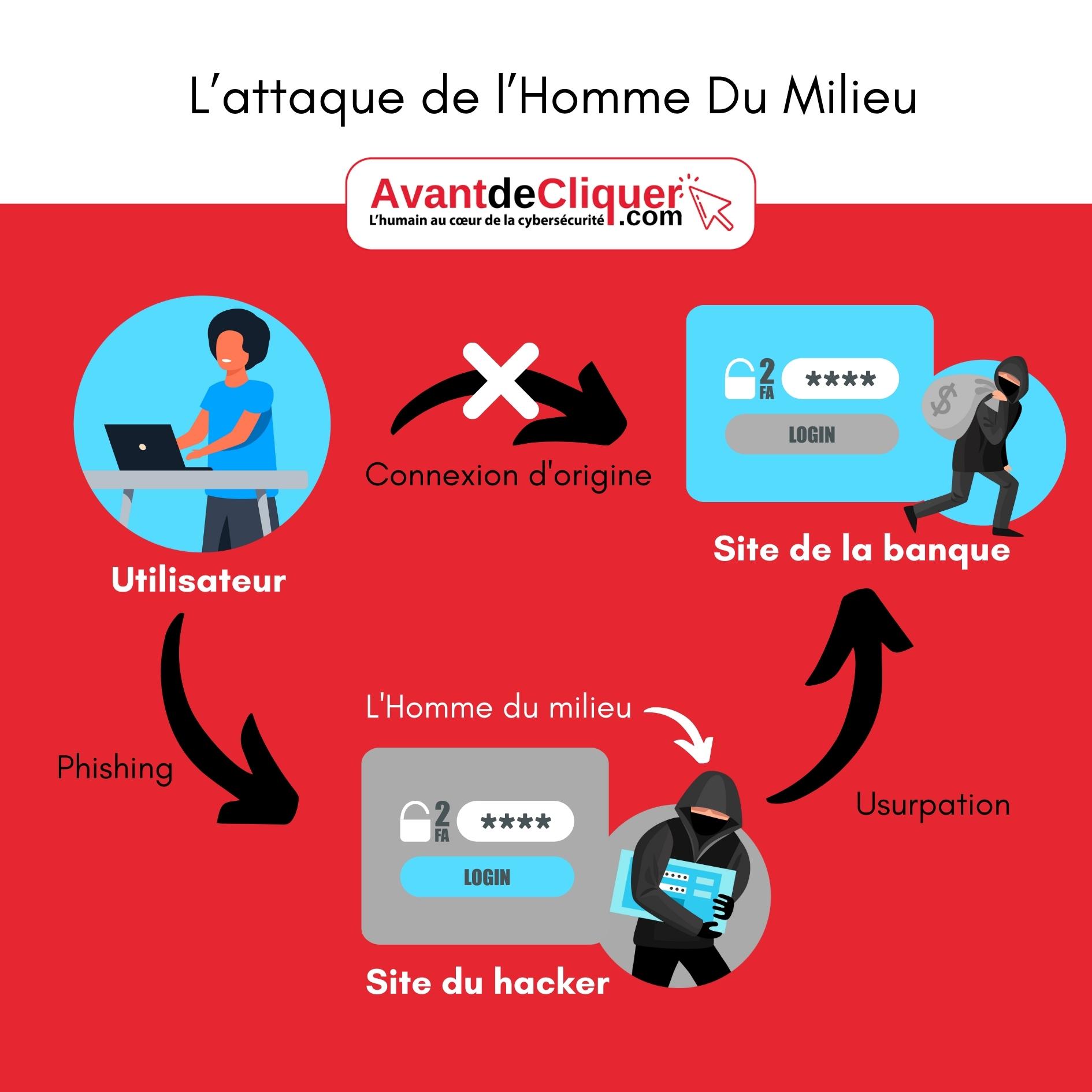
To bypass 2FA security and its multiple authentication levers, hackers use, among other things, the so-called "man-in-the-middle" (MITM) attack. man in the middle attack (MITM)
What is a man-in-the-middle attack?
The purpose of the Man-in-the-Middle attack in this scenario isto hijack communications between two parties, without either of them suspecting that the communication channel between them has been compromised.
A simple example in 5 steps:
- A user receives an email from phishingphishing that redirects them to a site identical to that of their bank, the hacker's site.
- The user enters their credentials (first factor).
- At the same time, the hacker's site attempts to log in to the real bank site using the credentials.
- As a result, the user receives the real code from their bank (second factor) via text message and enters it on the hacker's website.
- The hacker's site then only needs to use the second factor to log in to the real bank site.
Solutions to the risks of circumventing two-factor authentication
Implement a facial recognition system:
Adopting a two-step verification system that includes facial recognition is one of the most secure and complex methods of protection.
This involves replacing two-factor authentication with fingerprint, voice, or facial recognition.
Some facial biometrics systems use a static image of the user's face as a reference, but others go further by verifying identity using other methods.
This is achieved through the use of infrared technology and the creation of a 3D biometric algorithm or real-time video and smile and gesture analysis, ensuring that authentication and verification are completely secure.
This way, systems are protected against potential attacks using technologies such as deepfakes or 3D-printed masks.
Three-factor authentication
It already exists thanks to Google's Advanced Protection Program. In addition to a password, two physical keys are required to access your account. These keys replace the SMS verification process.
Let's go further with the AAA protocol
This protocol, which is already in use, is employed in IT security. It performs three functions:
- Authentication
- Authorization
- Traceability
As you can see, in addition to two-factor authentication, it enables traceability and therefore monitoring of connections and subsequent activities.
















